Cybersecurity News
Has WhatsApp become a potential career assassin? | Afua Hirsch
 The app helped connect me to an inspiring sisterhood. But the case of police officer Robyn Williams shows unopened messages can be a legal minefield
The app helped connect me to an inspiring sisterhood. But the case of police officer Robyn Williams shows unopened messages can be a legal minefieldWe need to talk about WhatsApp. When the little green speech bubble first showed up in my life, I greeted it with awe and wonder. I even wrote a little love letter to its ability to connect with a virtual black sisterhood – the kind that rarely exists in our too-undiverse workplaces in real life – in my first book. It became the perfect platform to share experiences, frustrations, strategies and ideas.
WhatsApp group communities proliferated on my phone – they were education, community and activism all in one place. It was great.
Continue reading...Be Alert this Holiday Season: Payment Security Tips for Businesses
On this blog we explore the challenges around security of payment data during the hectic holiday season and provide tips and best practices to help restaurants better secure their payment data. The following is a Q & A with Troy Leach, Senior Vice President of the PCI Security Standards Council and Laura Chadwick, Program Director, Technology & Innovation of the National Restaurant Association about the importance of cybersecurity this holiday season.
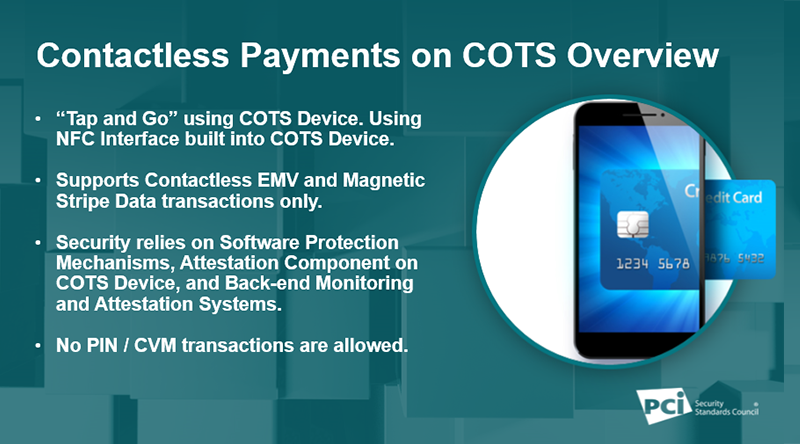
Just Published: PCI Contactless Payments on COTS
The PCI Security Standards Council (PCI SSC) has published a new data security standard for solutions that enable merchants to accept contactless payments using a smartphone or other commercial off-the-shelf (COTS) mobile device with near-field communication (NFC). Here’s what you need to know about the new PCI Contactless Payments on COTS (CPoC™) Standard and its supporting validation program.
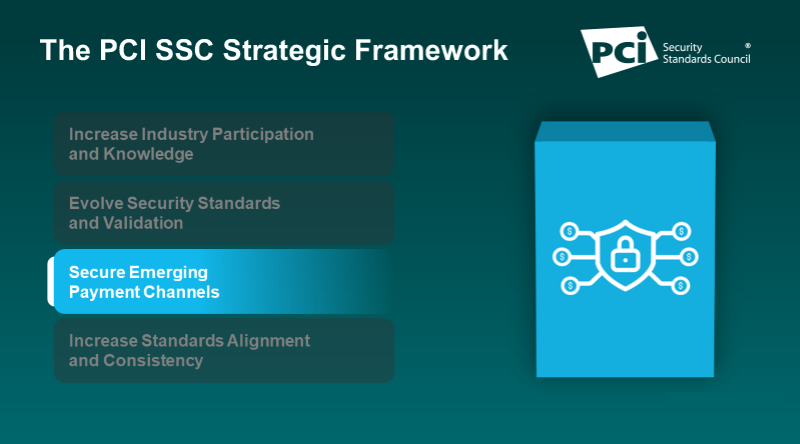
Securing Emerging Payment Channels
Securing emerging payment channels is a core pillar in the PCI Security Standards Council’s (PCI SSC) strategic framework, which guides how the Council achieves its mission and supports the needs of the global payments industry. In this interview with PCI SSC Standards Officer Emma Sutcliffe, we discuss this pillar and how it’s shaping Council priorities.
What sort of security software and backups do I need for a home business?

Allen wants to set up a small company working from home, and would like some advice
I’m looking to set up a small business working from home, and would like some advice on back up and security measures. I have an Office 365 account so my main directory for saving documents will be OneDrive. I was looking to back up on a Synology NAS drive, perhaps to two separate hard drives as a precaution. Also, I currently just use Windows’ built-in security, but wondered whether I should look for something else.
Initially, it would just be me, but if things go well then I may have another two or three people helping. I’m assuming I can just scale up any security measures as the need arises. Allen
Technology manufacturers cater to two very large markets with different needs: home users and businesses. You’re about to enter the SoHo (small office, home office) market where home technologies dominate because most single traders don’t need proper business systems with all the extra costs and complications involved.
Continue reading...Twitter to clear out inactive accounts and free up usernames

Company has been criticised for handling of move it says will reduce risk from hacking
Twitter has announced it is to clear out inactive accounts, freeing up dormant usernames and reducing the risk of old accounts being hacked.
But the company is facing criticism for the way it has handled the announcement, with many concerned that the accounts of people who have died over the past decade will be removed with no way of saving their Twitter legacies.
Continue reading...ISA in Practice Case Study: TIVIT
To better serve its customers in the payment card industry and support their PCI Data Security Standard (PCI DSS) compliance initiatives, TIVIT chose Internal Security Assessor (ISA) training and certification for its staff.
Google's secret cache of medical data includes names and full details of millions – whistleblower

Whistleblower tells Guardian of growing alarm over secret transfer of medical history data, which can be accessed by Google staff
A whistleblower who works in Project Nightingale, the secret transfer of the personal medical data of up to 50 million Americans from one of the largest healthcare providers in the US to Google, has expressed anger to the Guardian that patients are being kept in the dark about the massive deal.
Related: Mick Mulvaney drops impeachment lawsuit but will not comply with House subpoena – live
Continue reading...These new rules were meant to protect our privacy. They don’t work | Stephanie Hare
 The data protection laws introduced last year are failing us – and our children
The data protection laws introduced last year are failing us – and our childrenWho owns your data? This is one of the toughest questions facing governments, companies and regulators today and no one has answered it to anyone’s satisfaction. Not what we were promised last year, when the European Union’s General Data Protection Regulation, commonly known as the GDPR, came into effect.
The GDPR was billed as the gold standard of data protection, offering the strongest data rights in the world. It has forced companies everywhere to modify their operating models, often at great cost. It inspired the state of California to pass a similar law and where California leads, the rest of the US often follows; there have been calls for a federal version of the GDPR.
Most websites nudge us into clicking 'I consent' by making it harder for us not to
Advances in computing processing power and AI will allow those who have our data to do much more with it, and so with us
Continue reading...Alexis Bledel, Lil Wayne, and Nicki Minaj Make McAfee’s Most Dangerous Celebrity 2019 List
Not that McAfee! By William Knowles @c4i Senior Editor InfoSec News October 29, 2019 Actress Alexis Bledel, best known for her role as Rory Gilmore in network television’s “Gilmore Girls,” tops McAfee’s U.S. list of most dangerous celebrities to search for online. For the thirteenth year, McAfee researched which famous individuals generate the riskiest results […]Navy Information Warfare
By William Knowles @c4i Senior Editor InfoSec News October 29, 2019 As a ten-year regular volunteer at the USO O’Hare, there’s a sly grin on my face knowing all the U.S. Navy personnel featured in this video have visited the Terminal 2 center at least once in their careers and should make every InfoSec […]7-Eleven fuel app data breach exposes users' personal details

App users were able to see other customers’ data, including names, dates of birth and mobile numbers
The popular petrol-buying app run by 7-Eleven has suffered a data breach that allowed customers to view the names, email addresses, mobile numbers and dates of birth of other users.
The 7-Eleven fuel app, which the company said this week has been downloaded two million times, was taken offline for a matter of hours on Thursday after a customer alerted the company to the fact that he was able to access the personal information of several other customers via the app.
Continue reading...Police database flagged 9,000 cybercrime reports as 'security risk'

Reports were quarantined by software designed to protect fraud bureau’s computer system, watchdog told
Thousands of reports of cybercrime were quarantined on a police database instead of being investigated because software designed to protect the computer system labelled them a security risk.
The backlog at one point stretched to about 9,000 reports of cybercrime and fraud, some of them dating back to October last year. The reports had been made to Action Fraud and handed to the National Fraud Intelligence Bureau (NFIB), run by the City of London police.
Related: Plan for massive facial recognition database sparks privacy concerns
Related: Counter-terror police running secret Prevent database
Continue reading...Farewell the ‘porn block’ – a PR exercise but lousy policy | Amy Orben
 Without greater access to our online habits, politicians cannot frame laws for the digital age
Without greater access to our online habits, politicians cannot frame laws for the digital ageThe UK government’s porn block was a dead man walking for months, if not years. It is long overdue that this attempt to curb children’s access to online pornography is scrapped. Almost two years ago, a close colleague and I sat in a meeting with one of the policymakers who had recently been asked to implement the proposal. The pained look on his face when we queried his progress confirmed our suspicions that it was an impossible task. It was clear to many that the block could – and would – never come to pass.
The plan did not have just one achilles heel – it had many.
Scientists and other stakeholders cannot access information about what the population is actually doing online
Related: UK drops plans for online pornography age verification system
Continue reading...Thump Thump Thump, Housekeeping!
By William Knowles @c4i Senior Editor InfoSec News October 19, 2019 According to Jani-King, Cleanliness – it’s one of the most researched items when consumers are exploring where to stay for business or leisure. It builds customer loyalty, generates positive praise (via word of mouth and social media) and drives hotel profitability. Regardless of property size, brand […]EC-Council Website Defaced Twice In A Weekend [Updated]
By William Knowles @c4i Senior Editor InfoSec News February 23, 2014 [Updated] Today’s defacement of the EC-Council (the second time this weekend) by Eugene Belford (a.k.a. The Plague) threatens the compromise of the 60,000+ security professionals who currently hold CEH certifications. Individuals who have achieved EC-Council certifications include the US Army, the FBI, Microsoft, IBM, the United Nations, National […]Former National Security Agency / Booz Allen Contractor Edward Snowden is an (ISC)² member.
By William Knowles @c4i Senior Editor InfoSec News July 11, 2013 On July 4th, The New York Times reported NSA contractor Edward Snowden trained and certified as a Certified Ethical Hacker by the EC-Council, a certificate which has since been rescinded by the organization. After what could be called stall tactics with myself, the (ISC)² […]China has built 'massive global data-collection ecosystem' to boost its interests

Chinese use state-owned enterprises, local tech companies and foreign partnerships, ASPI report says
The Chinese government is sweeping up vast amounts of data from all around the world to bulwark the nation’s security, but most critically to secure the political future of the Communist party, a new report argues.
Engineering Global Consent, a policy brief by the Australian Strategic Policy Institute’s Dr Samantha Hoffman, argues that the Chinese party-state seeks to influence – and where possible control – global online and political environments so that public sentiment around the world is more favourable towards its interests. China has expanded its operations of influence into organisations such as universities in the UK, the US and Australia.
Related: Peter Dutton: China accuses home affairs minister of 'shocking' and 'malicious' slur
Sign up to receive the top stories from Guardian Australia every morning
Related: Australia's relationship with China in a 'terrible' state after Morrison's US visit, Labor says
Continue reading...Prevent database is secure but not secret | Letter
 Describing a documented database as ‘secret’ risks causing unjustified distrust in a multi-agency programme that seeks to protect those vulnerable to all forms of radicalisation and keep our communities safe, writes Chief Constable Simon Cole
Describing a documented database as ‘secret’ risks causing unjustified distrust in a multi-agency programme that seeks to protect those vulnerable to all forms of radicalisation and keep our communities safe, writes Chief Constable Simon ColeYour front-page lead (7 October) talks of a “secret” police Prevent database. It is not a very well kept “secret”; a quick online search brings up numerous references to its existence in public documents – and it is where the published annual referral statistics are sourced from. The Prevent pages on the National Police Chiefs’ Council website also refer to the fact Prevent officers keep records.
We do this for exactly the same purpose we document other forms of supportive safeguarding activity such as for child sexual exploitation, domestic abuse or human trafficking. It means we can be – and are – subject to oversight and accountability.
Continue reading...Scientists invent new technology to print invisible messages

Messages can only be seen under UV light and can be erased using a hairdryer
Forget lemon juice and hot irons, there is a new way to write and read invisible messages – and it can be used again and again.
The approach, developed by researchers in China, involves using water to print messages on paper coated with manganese-containing chemicals. The message, invisible to the naked eye, can be read by shining UV light on the paper.
Continue reading...