Cybersecurity News
38,000 people forced to pick up email passwords in person
Malware and legal requirements force academics and students to join a near-endless line in order to pick up their passwords
The post 38,000 people forced to pick up email passwords in person appeared first on WeLiveSecurity
38,000 people forced to pick up email passwords in person
Malware and legal requirements force academics and students to join a near-endless line in order to pick up their passwords
The post 38,000 people forced to pick up email passwords in person appeared first on WeLiveSecurity
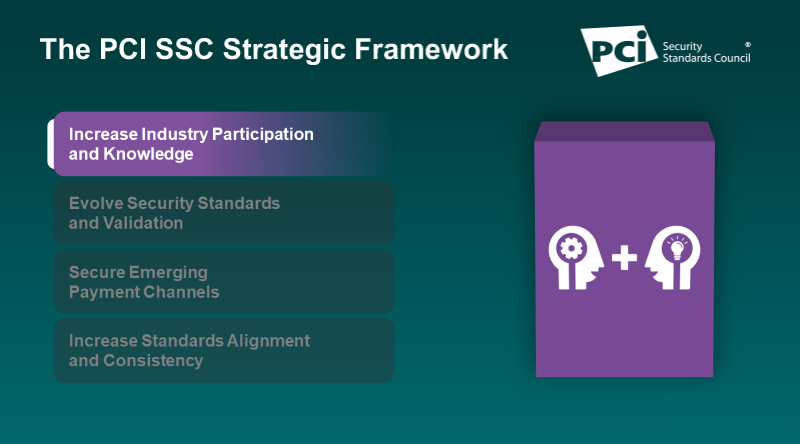
Increasing Industry Participation and Knowledge
Increasing industry participation and knowledge is a core pillar in the PCI Security Standards Council’s strategic framework, which guides how the Council achieves its mission and supports the needs of the global payments industry. To round out our Q&A blog series introducing the framework, we interview PCI SSC Executive Director Lance Johnson on this foundational strategic pillar and how it ties the framework together.
Nuclear Bot Author Arrested in Sextortion Case
Last summer, a wave of sextortion emails began flooding inboxes around the world. The spammers behind this scheme claimed they'd hacked your computer and recorded videos of you watching porn, and promised to release the embarrassing footage to all your contacts unless a bitcoin demand was paid. Now, French authorities say they've charged two men they believe are responsible for masterminding this scam. One of them is a 21-year-old hacker interviewed by KrebsOnSecurity in 2017 who openly admitted to authoring a banking trojan called "Nuclear Bot."It’s time to disconnect RDP from the internet
Brute-force attacks and BlueKeep exploits usurp convenience of direct RDP connections; ESET releases a tool to test your Windows machines for vulnerable versions
The post It’s time to disconnect RDP from the internet appeared first on WeLiveSecurity
It’s time to disconnect RDP from the internet
Brute-force attacks and BlueKeep exploits usurp convenience of direct RDP connections; ESET releases a tool to test your Windows machines for vulnerable versions
The post It’s time to disconnect RDP from the internet appeared first on WeLiveSecurity
Ransomware Gangs Now Outing Victim Businesses That Don’t Pay Up
As if the scourge of ransomware wasn't bad enough already: Several prominent purveyors of ransomware have signaled they plan to start publishing data stolen from victims who refuse to pay up. To make matters worse, one ransomware gang has now created a public Web site identifying recent victim companies that have chosen to rebuild their operations instead of acquiescing to their tormentors.The worst passwords of 2019: Did yours make the list?
These passwords may win the popularity contest but lose flat out in security
The post The worst passwords of 2019: Did yours make the list? appeared first on WeLiveSecurity
The worst passwords of 2019: Did yours make the list?
These passwords may win the popularity contest but lose flat out in security
The post The worst passwords of 2019: Did yours make the list? appeared first on WeLiveSecurity
Inside ‘Evil Corp,’ a $100M Cybercrime Menace
The U.S. Justice Department this month offered a $5 million bounty for information leading to the arrest and conviction of a Russian man indicted for allegedly orchestrating a vast, international cybercrime network that called itself "Evil Corp" and stole roughly $100 million from businesses and consumers. As it happens, for several years KrebsOnSecurity closely monitored the day-to-day communications and activities of the accused and his accomplices. What follows is an insider's look at the back-end operations of this gang.Dominic Cummings: If Leave had lost Brexit vote, I’d have queried result as invalid
 Boris Johnson aide wrote to data watchdog in 2017 complaining electoral system was ‘wide open to abuse’
Boris Johnson aide wrote to data watchdog in 2017 complaining electoral system was ‘wide open to abuse’Boris Johnson’s adviser Dominic Cummings would have challenged the EU referendum result as “invalid” had Vote Leave lost the Brexit campaign.
According to documents seen by the Observer, the prime minister’s chief aide told the UK’s data watchdog that he would have contested the result because UK elections are “wide open to abuse.”
Continue reading...Week in security with Tony Anscombe
ESET's Cybersecurity Trends 2020 report is out – New Chrome feature boosts account security – Hundreds of thousands of birth certificate applications leaked online
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
Week in security with Tony Anscombe
ESET's Cybersecurity Trends 2020 report is out – New Chrome feature boosts account security – Hundreds of thousands of birth certificate applications leaked online
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
2FA: Double down on your security
The second authentication factor might be a minor inconvenience, but it provides a major security boost
The post 2FA: Double down on your security appeared first on WeLiveSecurity
2FA: Double down on your security
The second authentication factor might be a minor inconvenience, but it provides a major security boost
The post 2FA: Double down on your security appeared first on WeLiveSecurity
P2PE v3.0: What Merchants Need to Know
The updates to the P2PE Standard and supporting program is part of the Council’s mission to evolve security standards and validation programs to support a range of environments, technologies and methodologies for achieving security. Ultimately, the updated PCI Point-to-Point Encryption (P2PE) ® Standard and supporting program will result in more PCI P2PE ® Solutions available to the marketplace. Here we cover key questions on what merchants need to know about P2PE v3.0.
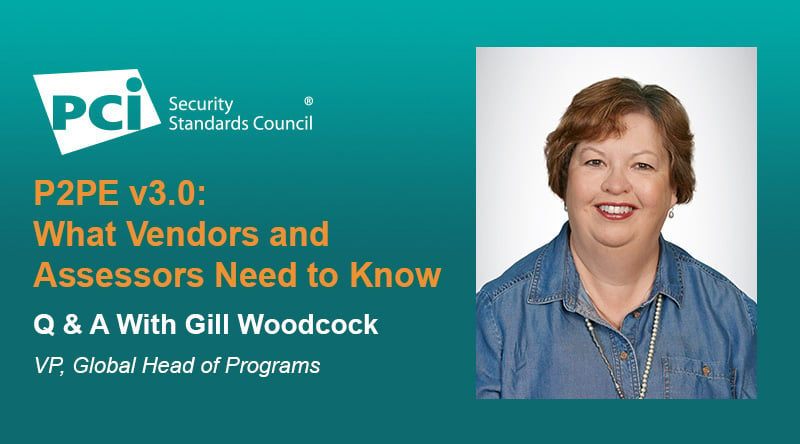
P2PE v3.0: What Vendors and Assessors Need to Know
The updates to the P2PE Standard and supporting program are part of the Council’s mission to evolve security standards and validation programs to support a range of environments, technologies and methodologies for achieving security. Ultimately, the updated PCI Point-to-Point Encryption (P2PE)® Standard and supporting program will result in more PCI P2PE®Solutions available to the marketplace. We sit down with PCI SSC Vice President, Global Head of Programs Gill Woodcock to discuss the changes to the program.
The Great $50M African IP Address Heist
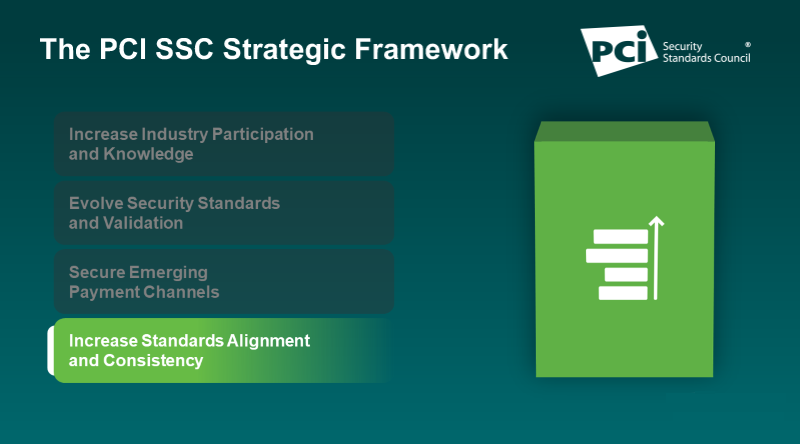
A top executive at the nonprofit entity responsible for doling out chunks of Internet addresses to businesses and other organizations in Africa has resigned his post following accusations that he secretly operated several companies which sold tens of millions of dollars worth of the increasingly scarce resource to online marketers. The allegations stemmed from a three-year investigation by a U.S.-based researcher whose findings shed light on a murky area of Internet governance that is all too often exploited by spammers and scammers alike.Increasing Standards Alignment and Consistency
Increasing standards alignment and consistency is a core pillar in the PCI Security Standards Council’s strategic framework, which guides how the Council achieves its mission and supports the needs of the global payments industry. In this interview with PCI SSC Operations Officer Mauro Lance, we discuss this strategic pillar and how it’s shaping Council priorities.
The Guardian view on Boris Johnson’s NHS plan: trading patient data | Editorial
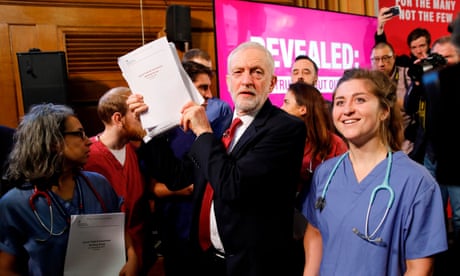 Donald Trump has made clear he wants a post-Brexit Britain to let US tech companies and big pharma access medical records
Donald Trump has made clear he wants a post-Brexit Britain to let US tech companies and big pharma access medical recordsThe NHS is a goldmine of patient data which the United States wants to be quarried by some of its biggest companies. Britain’s health service is home to a unique medical dataset that covers the entire population from birth to death. Jeremy Corbyn’s NHS press conference revealed that the US wanted its companies to get unrestricted access to the UK’s medical records, thought to be worth £10bn a year. A number of tech companies – including Google – already mine small parts of the NHS store. Ministers have been treading carefully after an attempt to create a single patient database for commercial exploitation was scrapped in 2016 when it emerged there was no way for the public to work out who would have access to their medical records or how they were using them.
However, such caution might be thrown to the wind if Boris Johnson gets his way over Brexit – and patients’ privacy rights are traded away for US market access. This would be a damaging step, allowing US big tech and big pharma to collect sensitive, personal data on an unprecedented scale. Donald Trump’s officials have already made clear that this is what they are aiming for. In the leaked government records of talks between US and UK trade representatives White House officials state that “the free flow of data is a top priority” in a post-Brexit world. Trump’s team see Brexit as an opportunity “to avoid forcing companies to disclose algorithms”. The US wants the UK to drop the EU’s 2018 data law, in which individuals must be told what is happening with their medical data, even if scrubbed of personal identifiers.
Continue reading...