Cybersecurity News
Malware developers turn to 'exotic' programming languages to thwart researchers
They are focused on exploiting pain points in code analysis and reverse-engineering.Podcast: IoT Piranhas Are Swarming Industrial Controls
 Enormous botnets of IoT devices are going after decades-old legacy systems that are rife in systems that control crucial infrastructure.
Enormous botnets of IoT devices are going after decades-old legacy systems that are rife in systems that control crucial infrastructure.
Babuk Ransomware Gang Ransomed, New Forum Stuffed With Porn
 A comment spammer flooded Babuk’s new ransomware forum with gay orgy porn GIFs and demanded $5K in bitcoin.
A comment spammer flooded Babuk’s new ransomware forum with gay orgy porn GIFs and demanded $5K in bitcoin.
Microsoft Rushes Fix for ‘PetitPotam’ Attack PoC
 Microsoft releases mitigations for a Windows NT LAN Manager exploit that forces remote Windows systems to reveal password hashes that can be easily cracked.
Microsoft releases mitigations for a Windows NT LAN Manager exploit that forces remote Windows systems to reveal password hashes that can be easily cracked.
PlugwalkJoe Does the Perp Walk
One day after last summer's mass-hack of Twitter, KrebsOnSecurity wrote that 22-year-old British citizen Joseph "PlugwalkJoe" O'Connor appeared to have been involved in the incident. When the Justice Department last week announced O'Connor's arrest and indictment, his alleged role in the Twitter compromise was well covered in the media. But most of the coverage so far seem to have overlooked the far more sinister criminal charges in the indictment, which involve an underground scene wherein young men turn to extortion, sextortion, SIM swapping, death threats and physical attacks -- all in a bid to seize control over highly-prized social media accounts.Malware Makers Using ‘Exotic’ Programming Languages
 Sprechen Sie Rust? Polyglot malware authors are increasingly using obscure programming languages to evade detection.
Sprechen Sie Rust? Polyglot malware authors are increasingly using obscure programming languages to evade detection.
The True Impact of Ransomware Attacks
 Keeper’s research reveals that in addition to knocking systems offline, ransomware attacks degrade productivity, cause organizations to incur significant indirect costs, and mar their reputations.
Keeper’s research reveals that in addition to knocking systems offline, ransomware attacks degrade productivity, cause organizations to incur significant indirect costs, and mar their reputations.
Twitter handle swatter jailed after victim dies following home raid
The 60-year-old victim's daughter believes he was "scared to death."WhatsApp chief says government officials, US allies targeted by Pegasus spyware
The officials were allegedly targeted in attacks dating back to 2019.Officials who are US allies among targets of NSO malware, says WhatsApp chief

Will Cathcart claims government officials around the world among 1,400 WhatsApp users targeted in 2019
Senior government officials around the world – including individuals in high national security positions who are “allies of the US” – were targeted by governments with NSO Group spyware in a 2019 attack against 1,400 WhatsApp users, according to the messaging app’s chief executive.
Will Cathcart disclosed the new details about individuals who were targeted in the attack after revelations this week by the Pegasus project, a collaboration of 17 media organisations which investigated NSO, the Israeli company that sells its powerful surveillance software to government clients around the world.
What is in the data leak?
Related: How does Apple technology hold up against NSO spyware?
Continue reading...Discord CDN and API Abuses Drive Wave of Malware Detections
 Targets of Discord malware expand far beyond gamers.
Targets of Discord malware expand far beyond gamers.
5 Steps to Improving Ransomware Resiliency
 Alex Restrepo, cybersecurity researcher at Veritas, lays out the key concepts that organizations should be paying attention to now and implementing today.
Alex Restrepo, cybersecurity researcher at Veritas, lays out the key concepts that organizations should be paying attention to now and implementing today.
Biden Administration Responds to Geopolitical Cyber Threats
In response to growing concerns regarding the recent uptick in large-scale, nation-state-backed ransomware attacks on critical infrastructure, the Biden administration is taking new action to tackle the evolving challenges posed by ransomware attacks.Week in security with Tony Anscombe
URL shortener services distributing Android malware – Week in security with Tony Anscombe
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
FIN7’s Liquor Lure Compromises Law Firm with Backdoor
 Using a lure relating to a lawsuit against the owner of Jack Daniels whiskey, the cybergang launched a campaign that may be bent on ransomware deployment.
Using a lure relating to a lawsuit against the owner of Jack Daniels whiskey, the cybergang launched a campaign that may be bent on ransomware deployment.
GitHub boosts supply chain security for Go modules
Go is now one of the most popular programming languages on the platform.Kaseya Obtains Universal Decryptor for REvil Ransomware
 The vendor will work with customers affected by the early July spate of ransomware attacks to unlock files; it's unclear if the ransom was paid.
The vendor will work with customers affected by the early July spate of ransomware attacks to unlock files; it's unclear if the ransom was paid.
The Pegasus project: why investigations like this are at the heart of the Guardian’s mission

Guardian editor-in-chief Katharine Viner reflects on our recent investigation into NSO Group, which sells hacking spyware used by governments around the world, and explains why journalism like this is so vital
When the Guardian’s head of investigations, Paul Lewis, first told me about a huge data leak suggesting authoritarian regimes were possibly using smartphone hacking software to target activists, politicians and journalists, perhaps the worst part is that I wasn’t particularly surprised.
Related: What is Pegasus spyware and how does it hack phones?
Related: Huge data leak shatters lie that the innocent need not fear surveillance
Related: The Pegasus project part 1: an invitation to Paris
Related: How you helped the Guardian report on the year that changed everything | Katharine Viner
Continue reading...How NSO became the company whose software can spy on the world
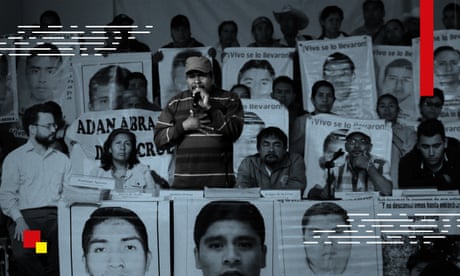
The Pegasus project has raised new concerns about the Israeli firm, which is a world leader in the niche surveillance market
In 2019, when NSO Group was facing intense scrutiny, new investors in the Israeli surveillance company were on a PR offensive to reassure human rights groups.
In an exchange of public letters in 2019, they told Amnesty International and other activists that they would do “whatever is necessary” to ensure NSO’s weapons-grade software would only be used to fight crime and terrorism.
What is in the data leak?
The Pegasus project is a collaborative journalistic investigation into the NSO Group and its clients. The company sells surveillance technology to governments worldwide. Its flagship product is Pegasus, spying software – or spyware – that targets iPhones and Android devices. Once a phone is infected, a Pegasus operator can secretly extract chats, photos, emails and location data, or activate microphones and cameras without a user knowing.
Show your support for the Guardian’s fearless investigative journalism today so we can keep chasing the truth
Continue reading...Protecting the hybrid workplace through Zero Trust security
The Zero Trust architecture offers an increasingly popular way to minimize cyber-risk in a world of hybrid cloud, flexible working and persistent threat actors.
The post Protecting the hybrid workplace through Zero Trust security appeared first on WeLiveSecurity
