Cybersecurity News
7 Infamous Moments in Adobe Flash's Security History
 End-of-life is here: Adobe's support for Flash is gone as of Jan. 1. Here's what we won't miss about the multimedia software platform.
End-of-life is here: Adobe's support for Flash is gone as of Jan. 1. Here's what we won't miss about the multimedia software platform.
Zero-Click Apple Zero-Day Uncovered in Pegasus Spy Attack
 The phones of 36 journalists were infected by four APTs, possibly linked to Saudi Arabia or the UAE.
The phones of 36 journalists were infected by four APTs, possibly linked to Saudi Arabia or the UAE.
Simplifying Proactive Defense With Threat Playbooks
 Fortinet's Derek Manky talks about how threat playbooks can equip defense teams with the tools they need to fight back against evolving attacker TTPs.
Fortinet's Derek Manky talks about how threat playbooks can equip defense teams with the tools they need to fight back against evolving attacker TTPs.
Dark Web Pricing Skyrockets for Microsoft RDP Servers, Payment-Card Data
 Underground marketplace pricing on RDP server access, compromised payment card data and DDoS-For-Hire services are surging.
Underground marketplace pricing on RDP server access, compromised payment card data and DDoS-For-Hire services are surging.
Critical Bugs in Dell Wyse Thin Clients Allow Code Execution, Client Takeovers
 The bugs rate 10 out of 10 on the vulnerability-severity scale, thanks to the ease of exploitation.
The bugs rate 10 out of 10 on the vulnerability-severity scale, thanks to the ease of exploitation.
Hacker Dumps Crypto Wallet Customer Data; Active Attacks Follow
 Customer data from a June attack against cryptocurrency wallet firm Ledger is now public and actively being used in attacks.
Customer data from a June attack against cryptocurrency wallet firm Ledger is now public and actively being used in attacks.
Cybersecurity Advent calendar: Stay aware, stay safe!
When it comes to holiday gifts, surprise and wonder are always welcome. When it comes to protecting your security, however, you don’t want to leave anything to chance.
The post Cybersecurity Advent calendar: Stay aware, stay safe! appeared first on WeLiveSecurity
We Have a National Cybersecurity Emergency -- Here's How We Can Respond
Let's prioritize bipartisan strategic actions that can ensure our national security and strengthen the economy. Here are five ideas for how to do that.A second hacking group has targeted SolarWinds systems
Some SolarWinds systems were found compromised with malware named Supernova and CosmicGale, unrelated to the recent supply chain attack.Telemed Poll Uncovers Biggest Risks and Best Practices
 What are the riskiest links in the virtual healthcare chain? Threatpost readers weigh in as part of an exclusive telemed poll.
What are the riskiest links in the virtual healthcare chain? Threatpost readers weigh in as part of an exclusive telemed poll.
Zero-click iOS zero-day found deployed against Al Jazeera employees
Zero-day exploited a vulnerability in the iMessages app, patched in iOS 14.iPhones vulnerable to hacking tool for months, researchers say

Analysis: NSO Group’s Pegasus spyware could allegedly track locations and access passwords
For almost a year, spyware sold by Israel’s NSO Group was allegedly armed with a computer security super-weapon: a zero-footprint, zero-click, zero-day exploit that used a vulnerability in iMessage to seize control of an iPhone at the push of a button.
That means it would have left no visible trace of being placed on target’s phones, could be installed by simply sending a message that the victim didn’t even need to click on, and worked even on phones that were running the then-latest version of iOS, the operating system for iPhones.
Continue reading...Firefox to ship 'network partitioning' as a new anti-tracking defense
Firefox's "network partitioning" feature to ship in v85, scheduled for January 2021.Cloud is King: 9 Software Security Trends to Watch in 2021
 Researchers predict software security will continue to struggle to keep up with cloud and IoT in the new year.
Researchers predict software security will continue to struggle to keep up with cloud and IoT in the new year.
Apple, Google, Microsoft, and Mozilla ban Kazakhstan's MitM HTTPS certificate
This marks the second time browsers makers had to intervene and block a certificate used by the Kazakhstan government to spy on its citizens.Microsoft Confirms Its Network Was Breached With Tainted SolarWinds Updates
 Attack on thousands of other companies as "moment of reckoning" for governments and industry, company president says.
Attack on thousands of other companies as "moment of reckoning" for governments and industry, company president says.
FBI Warns of DoppelPaymer Attacks on Critical Infrastructure
The operators behind DoppelPaymer have begun calling victims to pressure them into paying ransom, officials say.Sunburst’s C2 Secrets Reveal Second-Stage SolarWinds Victims
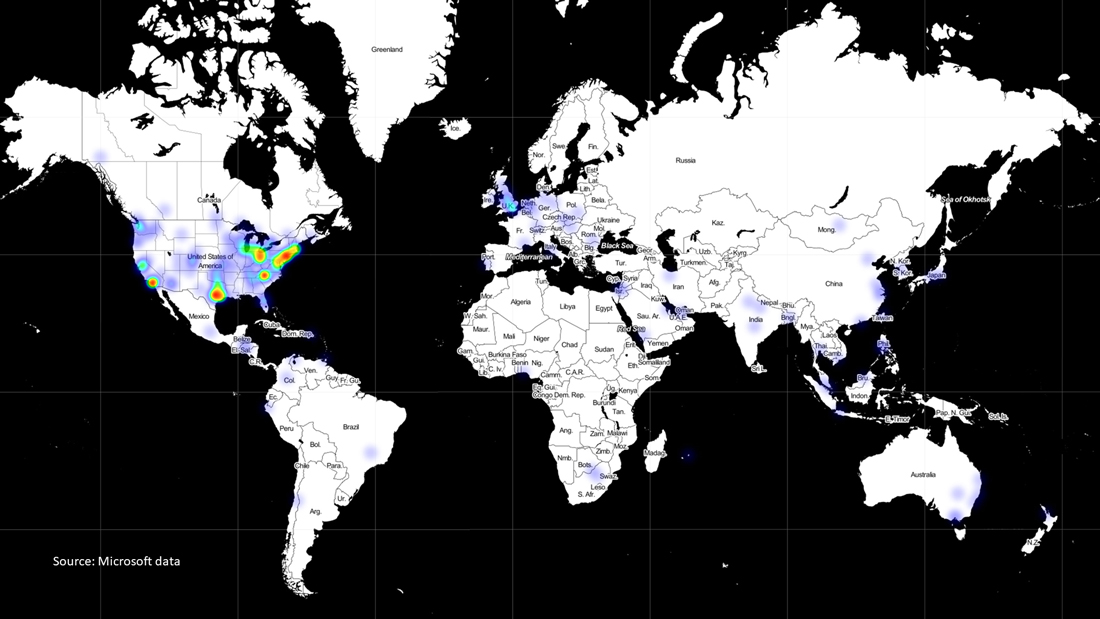
 Examining the backdoor's DNS communications led researchers to find a government agency and a big U.S. telco that were flagged for further exploitation in the spy campaign.
Examining the backdoor's DNS communications led researchers to find a government agency and a big U.S. telco that were flagged for further exploitation in the spy campaign.
