Cybersecurity News
Spam Kingpin Peter Levashov Gets Time Served
A federal judge in Connecticut today handed down a sentence of time served to spam kingpin Peter “Severa” Levashov, a prolific purveyor of malicious and junk email, and the creator of malware strains that infected millions of Microsoft computers globally. Levashov has been in federal custody since his extradition to the United States and guilty plea in 2018, and was facing up to 12 more years in prison. Instead, he will go free under three years of supervised release and a possible fine.Researchers: NSO Group’s Pegasus Spyware Should Spark Bans, Apple Accountability
 Our roundtable of experts weighs in on implications for Apple and lawmakers in the wake of the bombshell report showing widespread surveillance of dissidents, journalists and others.
Our roundtable of experts weighs in on implications for Apple and lawmakers in the wake of the bombshell report showing widespread surveillance of dissidents, journalists and others.
Back-to-Basics: Reduce Where Payment Data Can Be Found
As small and medium businesses begin to re-open following the pandemic, it’s important to do so securely in order to protect customer’s payment card data. Too often, data breaches happen as a result of vulnerabilities that are entirely preventable. The PCI Security Standards Council (PCI SSC) has developed a set of payment protection resources for small businesses. In this 8-part back-to-basics series, we highlight payment security basics for protecting against payment data theft. Today’s blog focuses on reducing where payment data can be found.
Law Firm to the Fortune 500 Breached with Ransomware
 Deep-pocketed clients' customers & suppliers could be in the attacker's net, with potential PII exposure from an A-list clientele such as Apple, Boeing and IBM.
Deep-pocketed clients' customers & suppliers could be in the attacker's net, with potential PII exposure from an A-list clientele such as Apple, Boeing and IBM.
Why Your Business Needs a Long-Term Remote Security Strategy
 Chris Hass, director of information security and research at Automox, discusses the future of work: A hybrid home/office model that will demand new security approaches.
Chris Hass, director of information security and research at Automox, discusses the future of work: A hybrid home/office model that will demand new security approaches.
16-Year-Old HP Printer-Driver Bug Impacts Millions of Windows Machines
 The bug could allow cyberattackers to bypass security products, tamper with data and run code in kernel mode.
The bug could allow cyberattackers to bypass security products, tamper with data and run code in kernel mode.
A New Security Paradigm: External Attack Surface Management
 Advanced EASM solutions are crucial to automating the discovery of the downstream third-party (or fourth-party, or fifth-party, etc.) IT infrastructures that your organization is exposed to, and may be vulnerable to attack, posing a critical risk for your organization.
Advanced EASM solutions are crucial to automating the discovery of the downstream third-party (or fourth-party, or fifth-party, etc.) IT infrastructures that your organization is exposed to, and may be vulnerable to attack, posing a critical risk for your organization.
MosaicLoader Malware Delivers Facebook Stealers, RATs
 The newly documented code is a full-service malware-delivery threat that's spreading indiscriminately globally through paid search ads.
The newly documented code is a full-service malware-delivery threat that's spreading indiscriminately globally through paid search ads.
Some URL shortener services distribute Android malware, including banking or SMS trojans
On iOS we have seen link shortener services pushing spam calendar files to victims’ devices.
The post Some URL shortener services distribute Android malware, including banking or SMS trojans appeared first on WeLiveSecurity
HP patches vulnerable driver lurking in printers for 16 years
Cyberattackers could exploit the bug to secure system-level privileges.Microsoft heads to court to take on imposter, homoglyph domains
Fake domains impersonating Microsoft are a thorn not only in the company's side but in that of its customers.What’s Next for REvil’s Victims?
 Podcast: Nothing, says a ransomware negotiator who has tips on staying out of the sad subset of victims left in the lurch, mid-negotiation, after REvil's servers went up in smoke.
Podcast: Nothing, says a ransomware negotiator who has tips on staying out of the sad subset of victims left in the lurch, mid-negotiation, after REvil's servers went up in smoke.
Unpatched iPhone Bug Allows Remote Device Takeover
 A format-string bug believed to be a low-risk denial-of-service issue turns out to be much nastier than expected.
A format-string bug believed to be a low-risk denial-of-service issue turns out to be much nastier than expected.
Law Firm for Ford, Pfizer, Exxon Discloses Ransomware Attack
Campbell Conroy & O'Neil reports the attack affected personal data including Social Security numbers, passport numbers, and payment card data for some individuals.Don’t Wanna Pay Ransom Gangs? Test Your Backups.
Browse the comments on virtually any story about a ransomware attack and you will almost surely encounter the view that the victim organization could have avoided paying their extortionists if only they'd had proper data backups. But the ugly truth is there are many non-obvious reasons why victims end up paying even when they have done nearly everything right from a data backup perspective.US Accuses China of Using Criminal Hackers in Cyber Espionage Operations
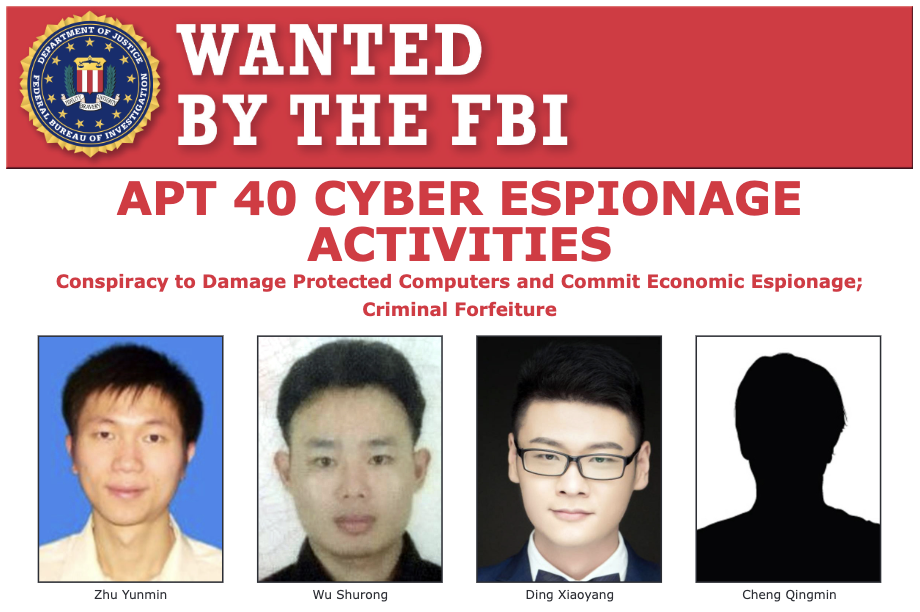 DOJ indicts four Chinese individuals for alleged role in attacks targeting intellectual property, trade secrets belonging to defense contractors, maritime companies, aircraft service firms, and others.
DOJ indicts four Chinese individuals for alleged role in attacks targeting intellectual property, trade secrets belonging to defense contractors, maritime companies, aircraft service firms, and others.
US Accuses China of Using Criminal Hackers in Cyber Espionage Operations
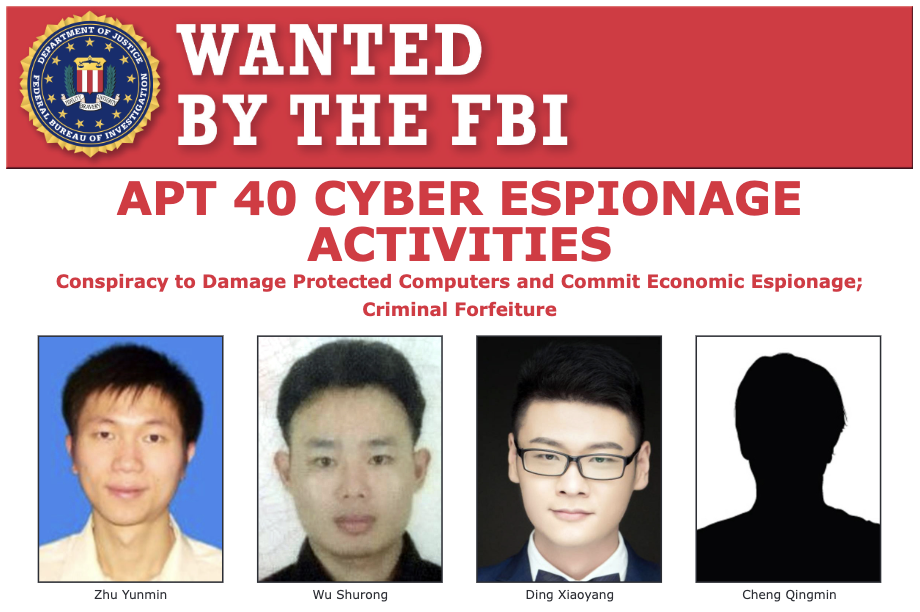 DOJ indicts four Chinese individuals for alleged role in attacks targeting intellectual property, trade secrets belonging to defense contractors, maritime companies, aircraft service firms, and others.
DOJ indicts four Chinese individuals for alleged role in attacks targeting intellectual property, trade secrets belonging to defense contractors, maritime companies, aircraft service firms, and others.
How Gaming Attack Data Aids Defenders Across Industries
 Web application attacks against the video game industry quadrupled in 2020 compared to the previous year, but companies outside entertainment can learn from the data.
Web application attacks against the video game industry quadrupled in 2020 compared to the previous year, but companies outside entertainment can learn from the data.
NSO Group Spyware Used On Journalists & Activists Worldwide
An investigation finds Pegasus spyware, intended for use on criminals and terrorists, has been used in targeted campaigns against others around the world.Ruthless Attackers Target Florida Condo Collapse Victims
 Hackers are stealing the identities of those lost in the condo-collapse tragedy.
Hackers are stealing the identities of those lost in the condo-collapse tragedy.