Cybersecurity News
Security bugs left unpatched in Android app with one billion downloads
The vulnerabilities impact SHAREit, an app used for sharing files between users and their devices.15 February 2021
Bluetooth Overlay Skimmer That Blocks Chip
As a total sucker for anything skimming-related, I was interested to hear from a reader working security for a retail chain in the United States that recently found bluetooth-enabled skimming devices placed over top of payment card terminals at several stores. Interestingly, these skimmers interfered with the terminal's ability to read chip-based cards, forcing customers to swipe the stripe instead.15 February 2021
Cybercrooks Rake in $304M in Romance Scams
 The number of people being targeted by fake relationship-seekers has spiked during the COVID-19 pandemic.
The number of people being targeted by fake relationship-seekers has spiked during the COVID-19 pandemic.
15 February 2021
France: Russian state hackers targeted Centreon servers in years-long campaign
New ANSSI report exposes new Sandworm APT attacks targeting IT companies using Centreon servers.15 February 2021
Record‑breaking number of vulnerabilities reported in 2020
High-severity and critical bugs disclosed in 2020 outnumber the sum total of vulnerabilities reported 10 years prior
The post Record‑breaking number of vulnerabilities reported in 2020 appeared first on WeLiveSecurity
15 February 2021
270 addreses are responsible for 55% of all cryptocurrency money laundering
Most cryptocurrency money laundering is concentrated in a few online services, opening the door for law enforcement actions.15 February 2021
270 addresses are responsible for 55% of all cryptocurrency money laundering
Most cryptocurrency money laundering is concentrated in a few online services, opening the door for law enforcement actions.15 February 2021
Malware Exploits Security Teams' Greatest Weakness: Poor Relationships With Employees
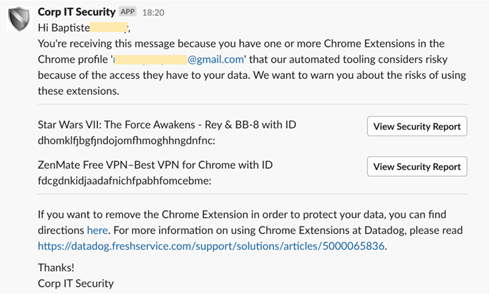 Users' distrust of corporate security teams is exposing businesses to unnecessary vulnerabilities.
Users' distrust of corporate security teams is exposing businesses to unnecessary vulnerabilities.
15 February 2021
100+ Financial Services Firms Targeted in Ransom DDoS Attacks in 2020
Consumer banks, exchanges, payment firms, and card issuing companies around the globe were among those hit.15 February 2021
How to Submit a Column to Dark Reading
 Have a new idea, a lesson learned, or a call to action for your fellow cybersecurity professionals? Here's how to submit your Commentary pieces to Dark Reading.
Have a new idea, a lesson learned, or a call to action for your fellow cybersecurity professionals? Here's how to submit your Commentary pieces to Dark Reading.
15 February 2021
Egregor ransomware operators arrested in Ukraine
Arrested suspects are believed to be clients of the Egregor RaaS, not the Egregor gang itself.14 February 2021
mHealth Apps Expose Millions to Cyberattacks
 Researcher testing of 30 mobile health apps for clinicians found that all of them had vulnerable APIs.
Researcher testing of 30 mobile health apps for clinicians found that all of them had vulnerable APIs.
12 February 2021
Yandex Data Breach Exposes 4K+ Email Accounts
 In a security notice, Yandex said an employee had been providing unauthorized access to users’ email accounts “for personal gain.”
In a security notice, Yandex said an employee had been providing unauthorized access to users’ email accounts “for personal gain.”
12 February 2021
Apple will proxy Safe Browsing traffic on iOS 14.5 to hide user IPs from Google
iOS 14.5 is currently in beta.12 February 2021
‘Annoyingly Believable’ Tax Scam Targets Mobile Users
 A well-crafted SMS phishing effort is harvesting personal data and credit-card details under the guise of offering tax refunds.
A well-crafted SMS phishing effort is harvesting personal data and credit-card details under the guise of offering tax refunds.
12 February 2021
Water Utility Hack Could Inspire More Intruders
If past cyberattacks are any indication, success begets imitation. In the wake of last week's hack of Florida water utility, other water utilities and users of remote desktop software would be wise to shore up defenses, experts say.12 February 2021
Singtel Suffers Zero-Day Cyberattack, Damage Unknown
 The Tier 1 telecom giant was caught up in a coordinated, wide-ranging attack using unpatched security bugs in the Accellion legacy file-transfer platform.
The Tier 1 telecom giant was caught up in a coordinated, wide-ranging attack using unpatched security bugs in the Accellion legacy file-transfer platform.
12 February 2021
Week in security with Tony Anscombe
ESET's Q4 2020 threat report is out – How smart sex toys can ruin your privacy – Protecting water supply systems
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
12 February 2021
Florida Water Plant Hack: Leaked Credentials Found in Breach Database
 Researchers discovered credentials for the Oldsmar water treatment facility in the massive compilation of data from breaches posted just days before the attack.
Researchers discovered credentials for the Oldsmar water treatment facility in the massive compilation of data from breaches posted just days before the attack.
12 February 2021
You've Got Cloud Security All Wrong: Managing Identity in a Cloud World
In a hybrid and multicloud world, identity is the new perimeter and a critical attack surface for bad actors.12 February 2021
